Barometer
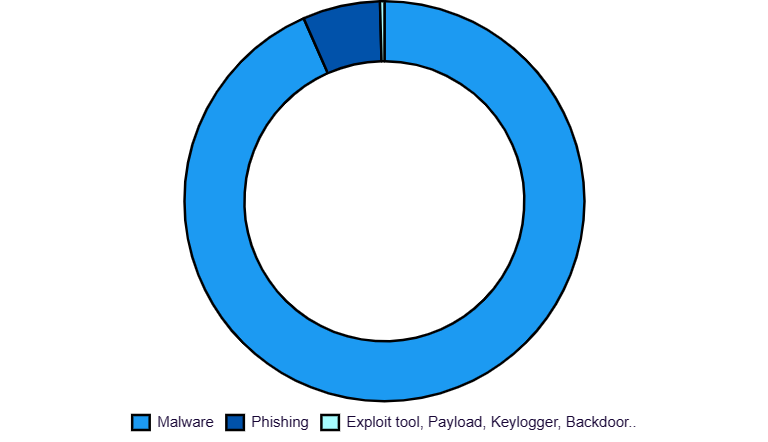
Indicateurs de compromission (IOCs) identifiés
Rapports de compromission identifiés (regroupement d’IoCs)

HIGHLIGHT OF THE MONTH
Software vendor Progress Software , has been in the news since early June after not one, but three critical CVEs (CVE-2023-34362, CVE-2023-35036 and CVE-2023-35708) were published on its MOVEit file transfer tool in the span of two weeks. Each of the three CVEs is an SQL injection vulnerability that allows unauthenticated access to publicly exposed MOVEit databases (T1190).
The CVE-2023-34362 has been widely exploited as part of a campaign to deploy the Clop ransomware, associated with the eponymous group whose business model is data encryption for ransom and Ransomware as a Service.
Through its dark net site , Clop has unveiled a list of all its victims, including names such as PWC and Sony, as well as numerous financial and legal services companies. However, as has already been observed with other threat actors such as LockBit, the group condemns the encryption of data from public health services and institutions.
Although patches were quickly deployed by Progress Software for the three CVEs, it is unlikely that all of the several thousand publicly exposed MOVEit instances reported by Censys have now been updated. The security company also notes a drop in the number of exposed MOVEit hosts since the vulnerabilities were announced, which could indicate that these services have been taken offline.

TOP

TOP
DEFINITION OF THE MONTH
Ransomware as a service (RAAS) is a business model used in cybercrime that involves buying a service from a criminal organisation in order to carry out ransomware attacks. There are 2 criminal profiles in these organisations:
The operator: the person in charge of all the development of the ransomware and the MCO (Maintenance in Operational Condition) of the attack infrastructures. They also provide after-sales service and can help affiliates with deployment or ransom negotiations. The affiliate can also offer a service to provide leaked identifiers to facilitate the first infection.
The affiliate: This is the customer, who will pay for access to the ransomware, and the attacker. They are generally responsible for customising the ransomware, compromising the victim’s assets, managing negotiations, etc.
The services provided by these cybercriminal companies are generally offered in the following forms:
- Monthly subscription
- Affiliate programme: monthly subscription with part of the ransom paid to the operator (e.g. lockbit)
- Single-use licence: a single use of the ransomware
- An affiliate profit-sharing scheme.
Whatever model is chosen, all affiliates are required to comply with what could be described as a set of internal rules. These include the characteristics and capabilities of the ransomware, a code of conduct for affiliates and a ban on targeting certain domains and/or countries. RaaS can therefore be seen as a kind of malware purchase/rental service with its own contracts and rules, making it a special division of cybercrime.

TOP
TOP
ABOUT THE CYBER THREATS BAROMETER
Malware, zero-day vulnerabilities, advanced persistent threats, industries and sectors particularly targeted, weak signals of emerging attacks…It’s no secret that knowledge of one’s adversary is a key factor for the security of an enterprise. The Cyber Threats Barometer gives you a monthly overview of the cyber threats detected in the previous month by Gatewatcher CTI , our Cyber Threat Intelligence platform.
Gatewatcher CTI’s automated collection, analysis and correlation engines are continuously fed by more than three thousand data sources from multiple channels: social networks, specialized sites, dark and deep web. They make threat information available an average of 24 hours in advance of the competition and help operational response teams make better decisions by dramatically reducing their analysis and incident treatment times.