CVE-2023-40044: Progress WS_FTP
TL ; DR : WS_FTP
Affected versions of WS_FTP software
- All versions prior to:
- 8.7.4
- 8.8.2
Deserialisation before authentication: WS_FTP vulnerabilities
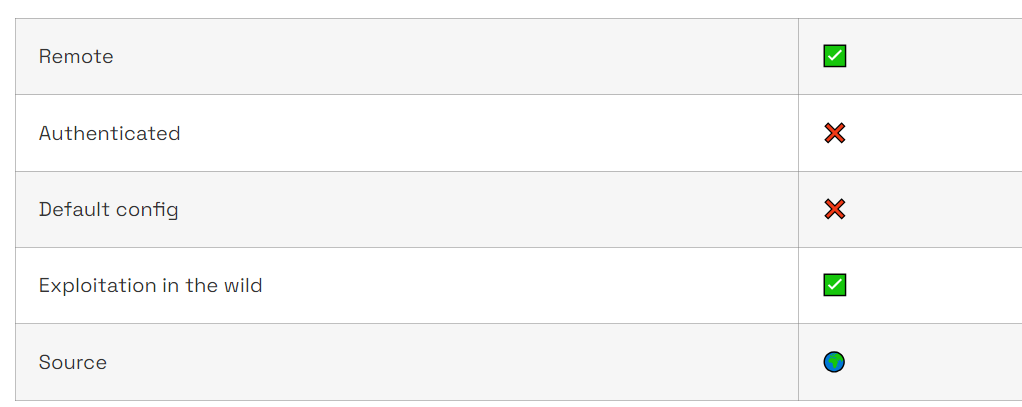
On September 27, 2023, the company Progress published a series of eight vulnerabilities ranging from medium (CVSS3.1: 5.3) to critical (CVSSv3.1: 10) concerning the WS_FTP software.
Although the company’s name may not be familiar, one of its products made headlines last June. Progress is also indeed, behind the MOVEit software, whose vulnerabilities published at the beginning of the summer were widely used to deploy the Cl0p ransomware.
Similarly to MOVEit, WS_FTP is a file transfer program. As its name suggests, it initially relies on the FTP protocol to carry out transfers. However, various modules are available to extend the product’s functionality. In particular, the Ad-Hoc Transfer module enables a file to be made available to a third party using a browser or Microsoft Outlook. This is the source of the CVE-2023-40044 vulnerability (CVSSv3.1: 10).
The vulnerability itself is relatively simple. It consists of deserialisation using a formatter that takes no precautions when processing input information.
Serialisation consists of transforming a data structure or an object into another format so that it can be stored or transmitted. Conversely, deserialisation transforms a sequence of bytes or a string of characters into an object or data structure.
However, if the data is not properly sanitised, it is possible to instantiate an object other than the one expected, leading to a denial of service (DoS) or remote code execution (RCE). This type of vulnerability is referenced by the MITRE as CWE-502.
According to the work published on this vulnerability, the formatter used here is a BinaryFormatter, which Microsoft warns against using in its documentation.
Detecting and resolving vulnerabilities
Since October 3, the CVE-2023-40044 vulnerability does not have a dedicated network detection rule (sid: 2048383).
This rule is based on the need not to have a filename but a name field in the request in order to follow the execution path leading to the vulnerability.
Nuclei templates have also been provided by the community to enable active verification.
Since the beginning of the month, this vulnerability has been observed on several occasions. The editor, having released the patches, strongly advises updating applications as soon as possible and, in the event that it is impossible to apply the patch, or if the version used is no longer supported, the editor recommends disabling the Ad-Hoc Transfer module.
Author: Purple Team Gatewatcher
Resources
- Progress advisory : https://community.progress.com/s/article/WS-FTP-Server-Critical-Vulnerability-September-2023
- Assetnote.io write-up : https://www.assetnote.io/resources/research/rce-in-progress-ws-ftp-ad-hoc-via-iis-http-modules-cve-2023-40044
- Nuclei template : https://github.com/ed-red/redmc_custom_templates_nuclei/blob/7303c5dbdb32fde46fba696ba0c8faedbc5f0b8b/http/cves/2023/CVE-2023-40044.yaml